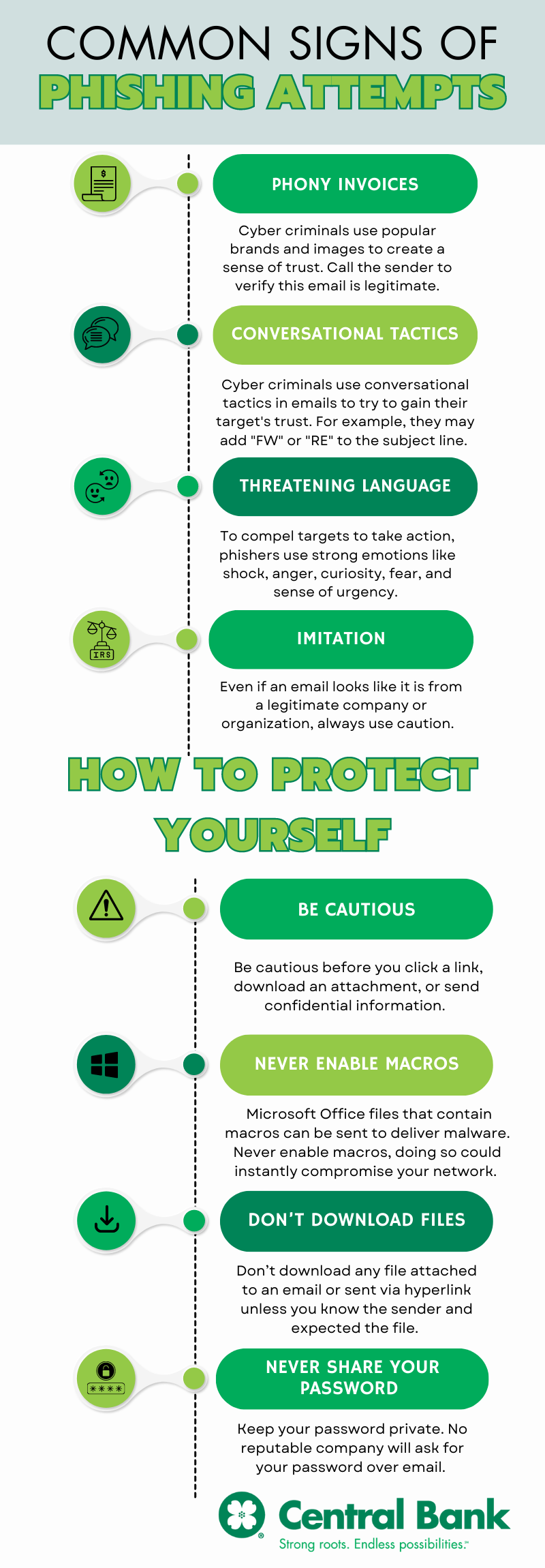
Phishing attempts are common these days, and it’s important to take steps to protect yourself and your sensitive information from falling into the wrong hands. Follow these tips to reduce the risk of falling victim to a phishing attack.
How to Identify a Phishing Email
-
Phony Invoices
Phony invoices are one of the most common lures in phishing scams. Cyber criminals use popular brands and images to create a sense of trust. You should call the sender to verify if the email is legitimate. -
Conversational Tactics
Cyber criminals use conversational tactics in emails to try to gain the target's trust. For example, they may add a “FW” or “RE” to the subject line. -
Urgent or Threatening Language
To encourage targets to take action, phishers use strong emotions like shock, anger, curiosity, fear, and a sense of urgency.
Read emails thoroughly before taking action. Beware of words like “Caution”, “Act Now”, and “Warning”, which are used to draw your attention and make you act quickly. Remember to slow down and keep your emotions in check before rushing to action. -
Imitation
Even if an email looks like it is from a legitimate company or organization, always use caution. Cyber criminals imitate company email addresses, signatures, and logos to build a false sense of trust.
Scammers may disguise themselves to be:
The IRS or other tax agencies: Around tax season, Cyber criminals send emails related to refunds or filing status, personal information, or PIN information. Even if you receive an email that looks legitimate, always use caution.
Popular companies: Be cautious of emails claiming to be from popular supply companies. If you have made a purchase recently, keep track of your orders so you know what emails to expect. Even if the message looks valid, go to the site directly to view the order information. If you haven’t made any purchases, never open emails that claim to have tracking information or an order confirmation.
How to Avoid Phishing Scams
-
Be Cautious
Appeals to curiosity can compel even the most security-conscious individuals to take action. Be cautious before you click a link, download an attachment, or send confidential information. -
Never Enable Macros
Cyber criminals send Microsoft Office files that contain macros to deliver malware. Never enable macros if prompted by an Office application. Doing so could instantly compromise your network. -
Don’t Download Files
Don’t download any file attached to an email or sent via hyperlink unless you know the sender and expected the file. -
Never Share Your Password
Keep your password private. No reputable company will ask for your password over email.
Trust your instincts. If you have a feeling something is wrong, it’s always safest to not open the email, click the link, or download the attachment. If you do receive a suspicious email or message, report it to the FTC at reportfraud.ftc.gov.